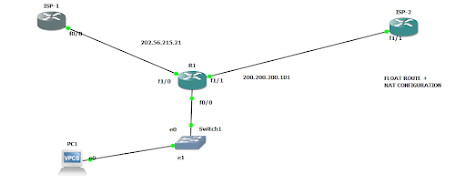
TOPOLOGY
GO TO ISP-1 ROUTER AND ENTER THIS COMMANDS IN CONFIGURATION TERMINAL MODE .
inter f0/0
ip address 202.56.215.1 255.255.255.0
ip address 202.56.215.1 255.255.255.0
no shutdown
exit
ip dhcp excluded-address 202.56.215.1 202.56.215.20
ip dhcp pool isp1
network 202.56.215.0 255.255.255.0
default-router 202.56.215.1
exit
inter loopback 0
ip address 8.8.8.8 255.0.0.0
no shutdown
exit
write
GO TO ISP- 2 ROUTER AND ENTER THIS COMMANDS IN CONFIGURATION TERMINAL MODE .
inter f1/1
ip address 200.200.200.1 255.255.255.0
ip address 200.200.200.1 255.255.255.0
no shutdown
exit
ip dhcp excluded-address 200.200.200.1 200.200.200.100
ip dhcp pool isp2
network 200.200.200.0 255.255.255.0
default-router 200.200.200.1
exit
inter loopback 0
ip address 8.8.8.8 255.0.0.0
no shutdown
exit
write
GO TO R1 ROUTER AND ENTER THIS COMMANDS IN CONFIGURATION TERMINAL MODE .
inter fa0/0
ip address 192.168.100.1 255.255.255.0
no shut
exit
inter f1/0
ip address dhcp
no shutdown
inter f1/1
ip address dhcp
no shut
ip dhcp pool manan
network 192.168.100.0 255.255.255.0
default-router 192.168.100.1
exit
ip route 0.0.0.0 0.0.0.0 202.56.215.1
ip route 0.0.0.0 .0.0.0.0 200.200.200.1
access-list 1 permit 192.168.100.0 0.0.0.255
route-map isp1
match ip address 1
match interface f1/0
route-map isp2
match ip address 1
match interface f1/1
ip nat inside source route-map isp1 interface f1/0 overload
ip nat inside source route-map isp2 interface f1/1 overload
inter f1/0
ip nat outside
inter f1/1
ip nat outside
inter f0/0
ip nat inside
GO TO VPC AND ENTER IS COMMAND FOR DHCP ADDRESS .
ip dhcp
Comments
Post a Comment