HISTORY OF TCP/IP MODEL
THE TCP/IP MODEL WAS DEVELOPED BY VINT CERF AND BOB KAHN IN THE 1970S. THEY WERE BOTH WORKING AT THE DEFENSE ADVANCED RESEARCH PROJECTS AGENCY (DARPA) AT THE TIME.
 |
| Vint Cerf And Bob Kahn |
CERF AND KAHN WERE TASKED WITH DEVELOPING A NEW NETWORK PROTOCOL THAT WOULD BE MORE RELIABLE AND EFFICIENT THAN THE EXISTING PROTOCOLS. THEY CAME UP WITH THE IDEA OF USING A LAYERED APPROACH, WHICH WOULD ALLOW EACH LAYER TO FOCUS ON A SPECIFIC TASK. THIS LED TO THE DEVELOPMENT OF THE TCP/IP MODEL, WHICH IS STILL THE BASIS FOR HOW DATA IS TRANSMITTED OVER THE INTERNET TODAY.
CERF AND KAHN ARE OFTEN REFERRED TO AS THE "FATHERS OF THE INTERNET" FOR THEIR WORK ON THE TCP/IP MODEL. THEY WERE INDUCTED INTO THE NATIONAL INVENTORS HALL OF FAME IN 2004 FOR THEIR CONTRIBUTIONS TO THE DEVELOPMENT OF THE INTERNET.
HERE ARE SOME OTHER NOTABLE PEOPLE WHO CONTRIBUTED TO THE DEVELOPMENT OF THE TCP/IP MODEL:
JON POSTEL: POSTEL WAS THE FIRST CHAIRMAN OF THE INTERNET ENGINEERING TASK FORCE (IETF), WHICH IS RESPONSIBLE FOR MAINTAINING AND EVOLVING THE TCP/IP PROTOCOL SUITE.
MIKE CORRIGAN: CORRIGAN WAS ONE OF THE
FIRST PEOPLE TO IMPLEMENT THE TCP/IP PROTOCOL ON A REAL NETWORK. HE DID THIS AT
THE UNIVERSITY OF CALIFORNIA, LOS ANGELES (UCLA) IN THE EARLY 1970S.
 |
| STEVE CROCKER |
STEVE CROCKER: CROCKER WAS ONE OF THE FIRST PEOPLE TO PROPOSE THE IDEA OF USING A LAYERED APPROACH TO NETWORK PROTOCOLS. HE ALSO DEVELOPED THE DOMAIN NAME SYSTEM (DNS), WHICH IS USED TO TRANSLATE DOMAIN NAMES INTO IP ADDRESSES.
______________
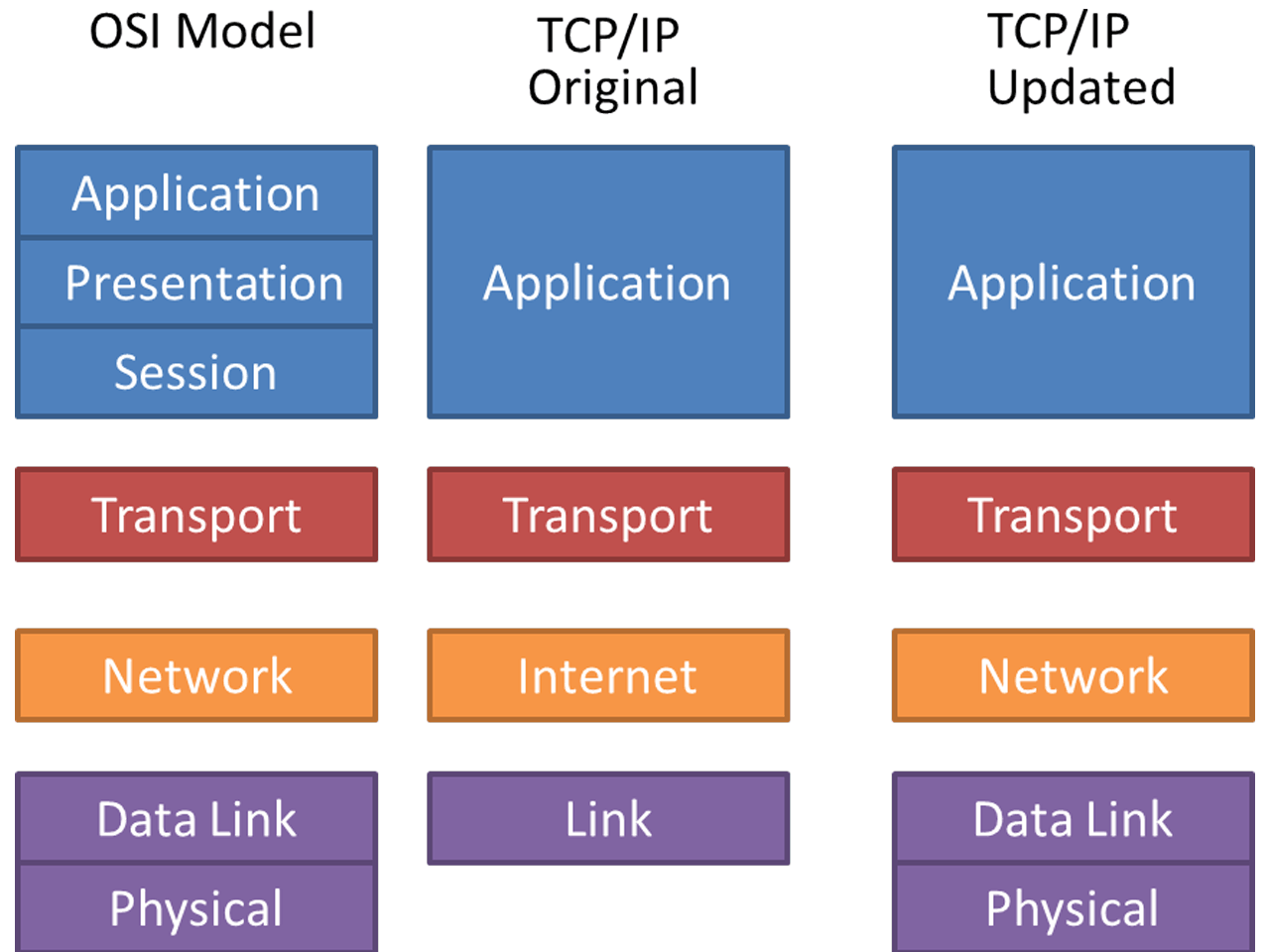
TCP/IP MODEL
THE TCP/IP MODEL IS A CONCEPTUAL MODEL THAT DESCRIBES HOW DATA IS TRANSMITTED OVER THE INTERNET. IT IS A FOUR-LAYER MODEL THAT DIVIDES NETWORK COMMUNICATIONS INTO FOUR DISTINCT CATEGORIES OR LAYERS. THE MODEL IS OFTEN REFERRED TO AS THE TCP/IP STACK.
THE FOUR LAYERS OF THE TCP/IP MODEL ARE:
APPLICATION LAYER:
THIS LAYER IS CLOSEST TO
THE END USER. IT IS RESPONSIBLE FOR PROVIDING SERVICES TO APPLICATIONS THAT
NEED TO COMMUNICATE OVER THE NETWORK. SOME OF THE PROTOCOLS THAT OPERATE AT
THIS LAYER INCLUDE HTTP, FTP, AND SMTP.
TRANSPORT LAYER:
THIS LAYER IS RESPONSIBLE
FOR PROVIDING RELIABLE END-TO-END COMMUNICATION BETWEEN APPLICATIONS. IT DOES
THIS BY BREAKING THE DATA UP INTO SMALLER UNITS CALLED SEGMENTS AND THEN
PROVIDING A MECHANISM FOR ENSURING THAT THE SEGMENTS ARE DELIVERED CORRECTLY.
SOME OF THE PROTOCOLS THAT OPERATE AT THIS LAYER INCLUDE TCP AND UDP.
INTERNET LAYER:
THIS LAYER IS RESPONSIBLE
FOR ROUTING DATA PACKETS ACROSS THE NETWORK. IT DOES THIS BY ASSIGNING EACH
PACKET A UNIQUE ADDRESS THAT IDENTIFIES THE DESTINATION OF THE PACKET. SOME OF
THE PROTOCOLS THAT OPERATE AT THIS LAYER INCLUDE IP AND ICMP.
LINK LAYER:
THIS LAYER IS RESPONSIBLE FOR
PROVIDING THE PHYSICAL CONNECTION BETWEEN DEVICES ON THE NETWORK. IT DOES THIS
BY DEFINING THE WAY THAT DATA IS TRANSMITTED OVER A PHYSICAL MEDIUM, SUCH AS AN
ETHERNET CABLE OR A WIRELESS SIGNAL. SOME OF THE PROTOCOLS THAT OPERATE AT THIS
LAYER INCLUDE ETHERNET AND PPP.
THE TCP/IP MODEL IS A HIERARCHICAL MODEL, WHICH MEANS THAT EACH LAYER RELIES ON THE LAYERS BELOW IT TO PERFORM ITS FUNCTION. FOR EXAMPLE, THE TRANSPORT LAYER CANNOT FUNCTION WITHOUT THE INTERNET LAYER, AND THE INTERNET LAYER CANNOT FUNCTION WITHOUT THE LINK LAYER.
THE TCP/IP MODEL IS A VERY IMPORTANT MODEL
FOR UNDERSTANDING HOW DATA IS TRANSMITTED OVER THE INTERNET. IT IS ALSO A VERY
IMPORTANT MODEL FOR UNDERSTANDING HOW DIFFERENT NETWORK PROTOCOLS WORK TOGETHER
TO PROVIDE RELIABLE AND EFFICIENT COMMUNICATION.
DIFFERENCE BETWEEN TCP/IP AND OSI MODEL LAYER
Comments
Post a Comment