A HIERARCHICAL NETWORK IS A NETWORK THAT IS DIVIDED INTO TWO
OR MORE LAYERS, WITH EACH LAYER HAVING A SPECIFIC FUNCTION. THIS TYPE OF
NETWORK DESIGN IS OFTEN USED IN LARGE AND COMPLEX NETWORKS, SUCH AS ENTERPRISE
NETWORKS AND THE INTERNET.
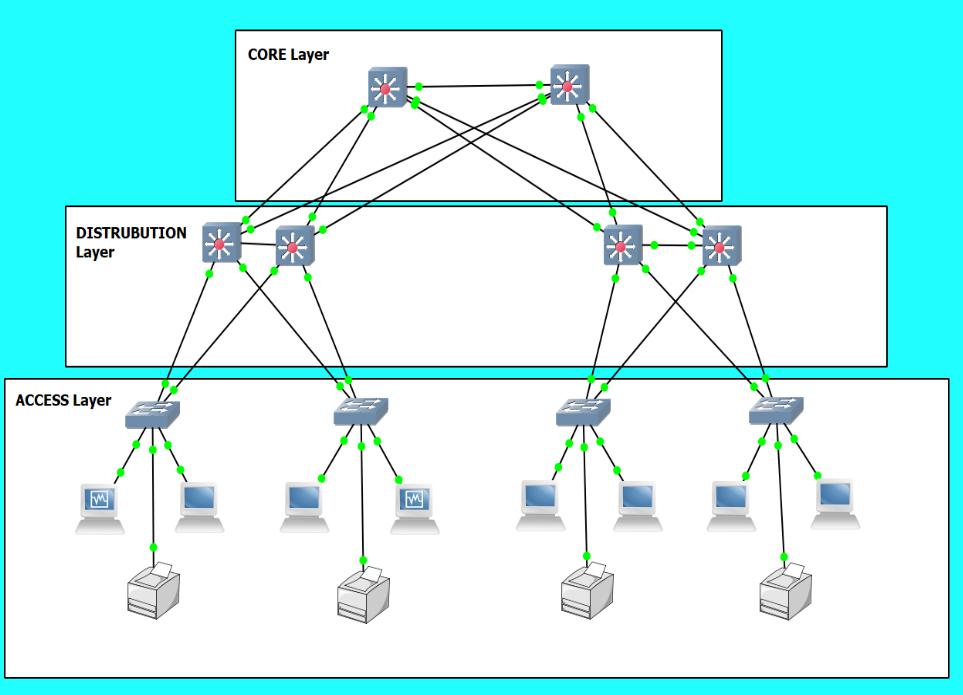
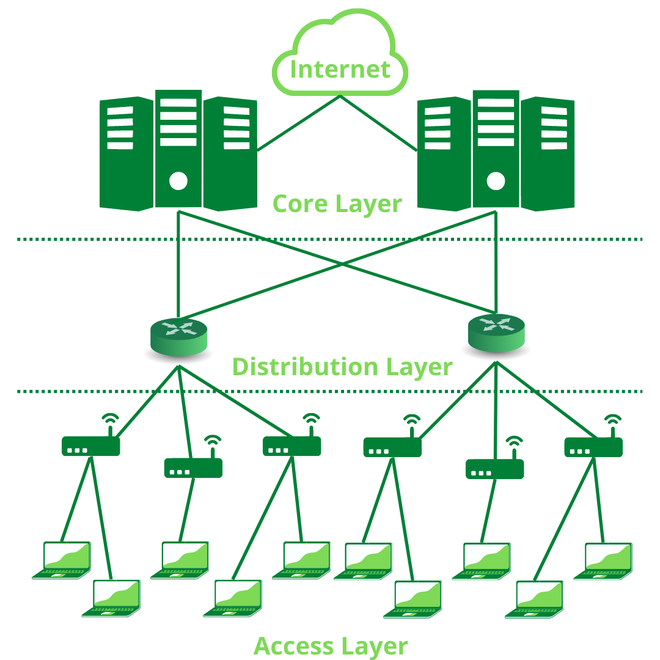
THE MOST COMMON HIERARCHICAL NETWORK DESIGN IS THE THREE-LAYER
MODEL, WHICH CONSISTS OF THE FOLLOWING LAYERS:
CORE LAYER:
THE CORE LAYER IS THE BACKBONE OF THE NETWORK AND PROVIDES
HIGH-SPEED CONNECTIVITY BETWEEN THE OTHER LAYERS. IT IS TYPICALLY MADE UP OF
HIGH-PERFORMANCE SWITCHES AND ROUTERS.
DISTRIBUTION LAYER:
THE DISTRIBUTION LAYER CONNECTS THE CORE LAYER TO THE ACCESS
LAYER. IT PROVIDES ROUTING AND SWITCHING SERVICES, AS WELL AS SECURITY AND
OTHER NETWORK SERVICES.
ACCESS LAYER:
THE ACCESS LAYER PROVIDES CONNECTIVITY TO END DEVICES, SUCH
AS COMPUTERS, PRINTERS, AND SERVERS. IT IS TYPICALLY MADE UP OF SWITCHES.
HIERARCHICAL NETWORKS OFFER A NUMBER OF ADVANTAGES OVER FLAT
NETWORKS, INCLUDING:
SCALABILITY:
HIERARCHICAL NETWORKS ARE MORE SCALABLE THAN FLAT NETWORKS,
MEANING THEY CAN BE EASILY EXPANDED TO ACCOMMODATE MORE DEVICES AND USERS.
PERFORMANCE:
HIERARCHICAL NETWORKS CAN PROVIDE BETTER PERFORMANCE THAN
FLAT NETWORKS BY REDUCING CONGESTION AND IMPROVING TRAFFIC FLOW.
SECURITY:
HIERARCHICAL NETWORKS CAN BE MORE SECURE THAN FLAT NETWORKS
BY ISOLATING DIFFERENT PARTS OF THE NETWORK AND IMPLEMENTING SECURITY POLICIES
AT EACH LAYER.
MANAGEABILITY:
HIERARCHICAL NETWORKS ARE EASIER TO MANAGE THAN FLAT
NETWORKS BECAUSE THEY ARE DIVIDED INTO SMALLER, MORE MANAGEABLE PARTS.
HERE ARE SOME EXAMPLES OF HIERARCHICAL NETWORKS:
A CORPORATE NETWORK WITH A CORE LAYER OF HIGH-PERFORMANCE
SWITCHES, A DISTRIBUTION LAYER OF ROUTERS AND SWITCHES, AND AN ACCESS LAYER OF
SWITCHES THAT CONNECT TO EMPLOYEE WORKSTATIONS AND PRINTERS.
A UNIVERSITY NETWORK WITH A CORE LAYER OF HIGH-PERFORMANCE
SWITCHES, A DISTRIBUTION LAYER OF ROUTERS AND SWITCHES, AND AN ACCESS LAYER OF
SWITCHES THAT CONNECT TO STUDENT AND FACULTY WORKSTATIONS, PRINTERS, AND OTHER
DEVICES.
A HOSPITAL NETWORK WITH A CORE LAYER OF HIGH-PERFORMANCE
SWITCHES, A DISTRIBUTION LAYER OF ROUTERS AND SWITCHES, AND AN ACCESS LAYER OF
SWITCHES THAT CONNECT TO PATIENT MONITORING EQUIPMENT, MEDICAL DEVICES, AND
OTHER DEVICES.
Comments
Post a Comment