WHAT IS CISCO
CISCO SYSTEMS, INC., COMMONLY KNOWN AS CISCO, IS AN AMERICAN MULTINATIONAL TECHNOLOGY CONGLOMERATE HEADQUARTERED IN SAN JOSE, CALIFORNIA. CISCO DEVELOPS, MANUFACTURES, AND SELLS NETWORKING HARDWARE, SOFTWARE, TELECOMMUNICATIONS EQUIPMENT AND OTHER HIGH-TECHNOLOGY SERVICES AND PRODUCTS. CISCO SPECIALIZES IN SPECIFIC TECH MARKETS, SUCH AS THE INTERNET OF THINGS (IOT), DOMAIN SECURITY, VIDEOCONFERENCING, AND ENERGY MANAGEMENT WITH LEADING PRODUCTS INCLUDING WEBEX, OPENDNS, JABBER, DUO SECURITY, AND JASPER. CISCO IS ONE OF THE LARGEST TECHNOLOGY COMPANIES IN THE WORLD RANKING 74 ON THE FORTUNE 100 WITH OVER $51 BILLION IN REVENUE AND NEARLY 80,000 EMPLOYEES.
CISCO'S PRODUCTS AND SERVICES ARE USED BY BUSINESSES OF ALL SIZES, GOVERNMENTS, AND EDUCATIONAL INSTITUTIONS AROUND THE WORLD. THE COMPANY'S NETWORKING PRODUCTS ARE USED TO CONNECT COMPUTERS, SERVERS, AND OTHER DEVICES TOGETHER TO FORM NETWORKS. CISCO'S SECURITY PRODUCTS ARE USED TO PROTECT NETWORKS FROM CYBERATTACKS. CISCO'S COLLABORATION PRODUCTS ARE USED TO ENABLE VIDEO CONFERENCING, INSTANT MESSAGING, AND OTHER FORMS OF COMMUNICATION. CISCO'S CLOUD MANAGEMENT PRODUCTS ARE USED TO MANAGE AND MONITOR CLOUD-BASED APPLICATIONS AND SERVICES.
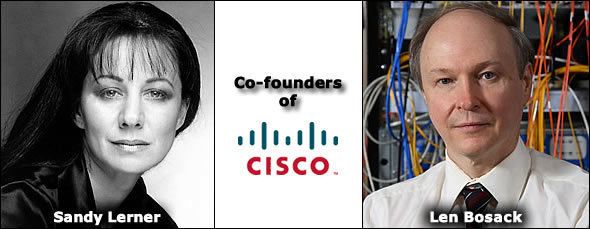
CISCO WAS FOUNDED IN 1984 BY LEONARD BOSACK AND SANDY LERNER. THE COMPANY'S NAME IS A PLAY ON THE WORD "SAN FRANCISCO". CISCO'S EARLY PRODUCTS WERE NETWORKING ROUTERS, WHICH WERE USED TO CONNECT COMPUTERS TOGETHER OVER LARGE DISTANCES. CISCO'S ROUTERS BECAME VERY POPULAR AND THE COMPANY QUICKLY GREW. IN THE 1990S, CISCO EXPANDED ITS PRODUCT LINE TO INCLUDE OTHER NETWORKING PRODUCTS, SUCH AS SWITCHES, FIREWALLS, AND WIRELESS ACCESS POINTS. CISCO ALSO BEGAN TO OFFER SOFTWARE AND SERVICES THAT COMPLEMENTED ITS HARDWARE PRODUCTS.
CISCO'S GROWTH CONTINUED IN THE 2000S AND 2010S. THE COMPANY'S PRODUCTS AND SERVICES BECAME INCREASINGLY IMPORTANT AS THE INTERNET BECAME MORE WIDESPREAD. CISCO ALSO EXPANDED ITS REACH INTO NEW MARKETS, SUCH AS THE CLOUD COMPUTING MARKET. TODAY, CISCO IS ONE OF THE MOST WELL-KNOWN AND RESPECTED TECHNOLOGY COMPANIES IN THE WORLD.
HERE ARE SOME OF THE MOST POPULAR CISCO PRODUCTS AND SERVICES:
NETWORKING PRODUCTS
ROUTERS, SWITCHES,
FIREWALLS, WIRELESS ACCESS POINTS, AND NETWORK MANAGEMENT SOFTWARE
SECURITY PRODUCTS
FIREWALLS, INTRUSION
DETECTION SYSTEMS, AND SECURITY SOFTWARE
COLLABORATION PRODUCTS
VIDEO CONFERENCING,
INSTANT MESSAGING, AND UNIFIED COMMUNICATIONS SOFTWARE
CLOUD MANAGEMENT PRODUCTS
CLOUD COMPUTING
PLATFORMS AND SERVICES
IOT PRODUCTS
NETWORKING AND SECURITY
PRODUCTS FOR THE INTERNET OF THINGS.

Comments
Post a Comment