WHAT IS SERVER
A SERVER IS A COMPUTER PROGRAM OR DEVICE THAT PROVIDES A SERVICE TO ANOTHER COMPUTER PROGRAM AND ITS USER, ALSO KNOWN AS THE CLIENT. THIS ARCHITECTURE IS CALLED THE CLIENT-SERVER MODEL.
A SERVER IS A NETWORK DEVICE BECAUSE IT IS A COMPUTER THAT IS CONNECTED TO A NETWORK AND PROVIDES RESOURCES TO OTHER COMPUTERS ON THE NETWORK. SERVERS ARE USED TO STORE DATA, RUN APPLICATIONS, AND PROVIDE SERVICES TO CLIENTS.
A SERVER IS A COMPUTER THAT PROVIDES RESOURCES, SUCH AS FILES, PROGRAMS, AND PRINTERS, TO OTHER COMPUTERS OVER A NETWORK.
IT IS A CENTRAL POINT FOR DATA STORAGE AND PROCESSING, AND IT CAN BE USED TO RUN APPLICATIONS, HOST WEBSITES, AND PROVIDE EMAIL SERVICES.
TYPES OF SERVER
WEB SERVERS
WEB SERVERS DELIVER WEB PAGES TO USERS' BROWSERS. THEY ARE RESPONSIBLE FOR STORING AND RETRIEVING WEB FILES, SUCH AS HTML, CSS, AND JAVASCRIPT.
FILE SERVERS
FILE SERVERS STORE FILES THAT CAN BE ACCESSED BY OTHER COMPUTERS ON THE NETWORK. THEY ARE OFTEN USED TO STORE SHARED DOCUMENTS, IMAGES, AND VIDEOS.
APPLICATION SERVERS
APPLICATION SERVERS RUN APPLICATIONS THAT ARE ACCESSED BY USERS OVER THE NETWORK. THEY ARE RESPONSIBLE FOR HANDLING THE PROCESSING AND DATA STORAGE REQUIREMENTS OF THE APPLICATIONS.
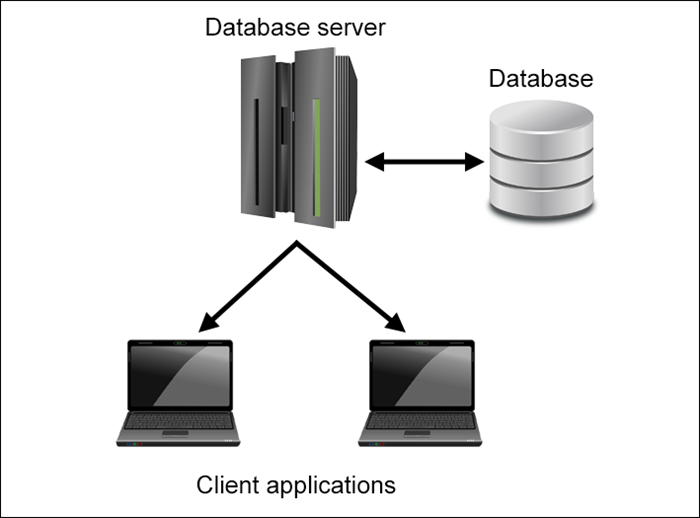
DATABASE SERVERS
DATABASE SERVERS STORE AND MANAGE DATABASES. THEY ARE USED TO STORE LARGE AMOUNTS OF DATA THAT CAN BE ACCESSED BY MULTIPLE USERS.
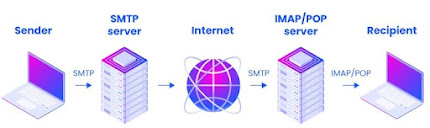
MAIL SERVERS
MAIL SERVERS SEND AND RECEIVE EMAIL MESSAGES. THEY ARE RESPONSIBLE FOR STORING EMAIL MESSAGES, ROUTING THEM TO THEIR DESTINATIONS, AND DELIVERING THEM TO USERS' MAILBOXES.
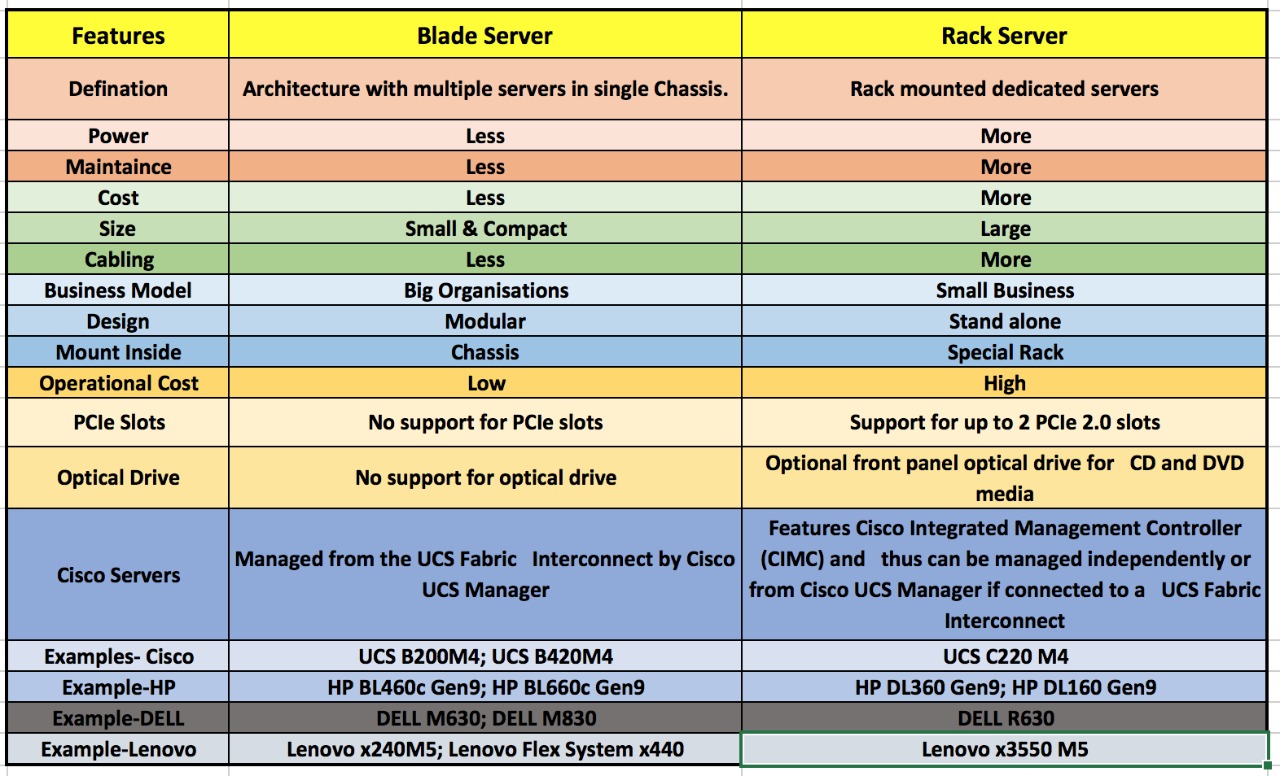
DIFFERENCE BETWEEN RACK AND BLADE SERVER
_______________
DHCP SERVER
A DHCP SERVER IS A NETWORK SERVER THAT AUTOMATICALLY PROVIDES AND ASSIGNS IP ADDRESSES, DEFAULT GATEWAYS AND OTHER NETWORK PARAMETERS TO CLIENT DEVICES.
IT RELIES ON THE STANDARD PROTOCOL KNOWN AS DYNAMIC HOST CONFIGURATION PROTOCOL OR DHCP TO RESPOND TO BROADCAST QUERIES BY CLIENTS.
TFTP SERVER
TRIVIAL FILE TRANSFER PROTOCOL (TFTP) IS A SIMPLE PROTOCOL THAT PROVIDES BASIC FILE TRANSFER FUNCTION WITH NO USER AUTHENTICATION.
TFTP IS BEST WHEN TRANSFERRING DATA LOCALLY WITHIN A DATA CENTER WHERE SECURITY AND NETWORK STABILITY IS NOT AN ISSUE.
ONE OF THE MAIN ADVANTAGES OF USING TFTP BOOT IS ITS SIMPLICITY AND SPEED. TFTP IS A VERY SIMPLE PROTOCOL THAT DOES NOT REQUIRE ANY AUTHENTICATION, ENCRYPTION, OR ERROR CORRECTION.
TFTP PORT NO IS 69.______________DNS SERVER
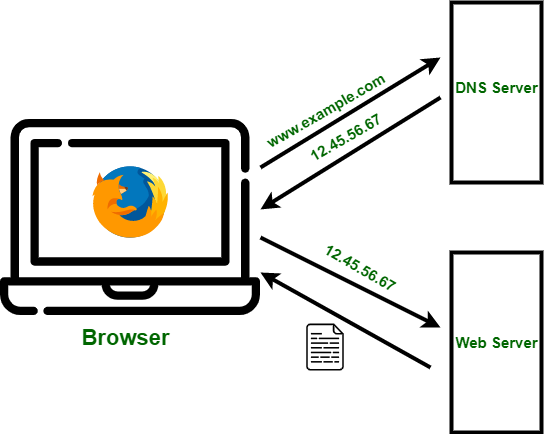
A DNS (DOMAIN NAME SYSTEM) SERVER IS A
CRITICAL COMPONENT OF THE INTERNET INFRASTRUCTURE THAT TRANSLATES
HUMAN-FRIENDLY DOMAIN NAMES (LIKE WWW.EXAMPLE.COM) INTO THE NUMERICAL IP
ADDRESSES (LIKE 192.0.2.1) THAT COMPUTERS USE TO COMMUNICATE WITH EACH OTHER.
DNS PORT NO IS 53.
A DNS (DOMAIN NAME SYSTEM) SERVER IS A
CRITICAL COMPONENT OF THE INTERNET INFRASTRUCTURE THAT TRANSLATES
HUMAN-FRIENDLY DOMAIN NAMES (LIKE WWW.EXAMPLE.COM) INTO THE NUMERICAL IP
ADDRESSES (LIKE 192.0.2.1) THAT COMPUTERS USE TO COMMUNICATE WITH EACH OTHER.
DNS PORT NO IS 53.




Comments
Post a Comment