Q2.
How to Build Up Networks in Real Environment ?
ANSWER :
Through Cables And RJ45
Connectors Buildes A Real Envoirment Network.
Like A Local Area Network.
SOME POINTS RELATED FOR CREAT NETWORK
1.
You Must Have Ethernet Cable
Which Will Help You Transfer Your Data Between Devices.
2.
You Should Be Able To Plug
In An Rj45 Connector.
3.
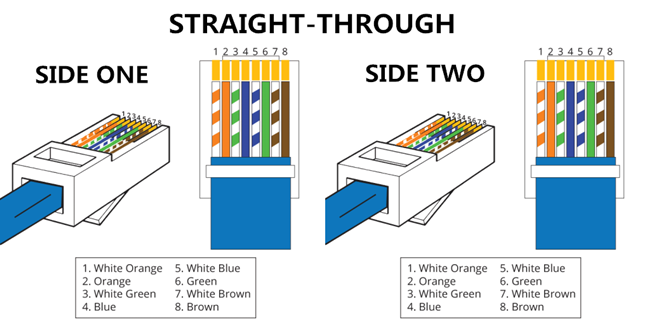
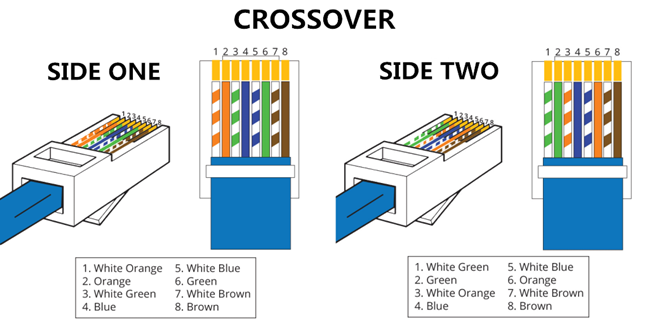
There Are Two Types Of Ethernet Cables. 1.
Straight Cable And 2. Crossover Cable.
Straight Cable :
Connect Different Devices Together.
Crossover Cable :
Connects The Same Devices Together.
Straight Cable Colour Coding : White Orange , Orange
. White Green , Blue . White Blue , Green . White brown , Brown.
Crossover Cable Colour Coding : White Green, Green . White Orange , Blue . White Blue , Orange . White Brown , Brown.
_______________
STRAIGHT CABLE
Comments
Post a Comment