CISCO SWITCHECLI INTERFACE HIS 3 MODE
1.USER MODE
switch>
2. ENABLE MODE
switch#
3. CONFIGURATION TERMINAL MODE
switch(config)#
_________________________
WHEN FIRST TIME ROUTER HIS OPEN THE FIST MODE HIS APPEARS
switch> AND WHEN TO ENABLE MODE TO ENTER switch> enable
SEE TO ENABLE MODE switch#
AND WHEN TO CONFIGURATION MODE TO ENTER switch# config t
AND SEE THE CONFIGURATION MDE switch(config)#
_______________________
THE PURPOSE OF ENABLE MODE IS ALL THE CONFIGURATION YOU PERFORMS A SWITCH TO SEE IT AND ANY IP PING IN ENABLE MODE
AND CHECK COMMUNICATION.
THE PURPOSE OF CONFIGURATION TERMINAL MODE ALL THE PROTOCOLS AND CONFIGURATION POERFORMED HIS MODE.
_________________________
WHAT IS VLAN
DEVIDED SINGLE BROADCAST DOMAIN INTO LOGICALLY MULTYPAL BROADCAST DOMAINS IS CALLED VLAN.
THE VIRTUAL LOCAL AREA NATWORK IS LAN CONFIGURED NOT BY PHYSICAL WIRING LIKE CONVENTIONAL LAN BUT IS CONFIGURED BY SWITCHES.
THERE
ARE 32 BITS IN A VLAN HEADER. THIS IS BROKEN DOWN AS FOLLOWS:
TPID
(TAG PROTOCOL IDENTIFIER): 16 BITS
PCP
(PRIORITY CODE POINT): 3 BITS
DEI
(DROP ELIGIBLE INDICATOR): 1 BIT
VID
(VLAN IDENTIFIER): 12 BITS
BENEFIT OF VLAN
1. SECURITY PURPOSE.
2. CONTROLL BROADCASTING.
ADDVANTAGES OF VLAN
1. REDUCTION IN COST
2. SAVING OF TIME REQURID FOR REWIRING
3. VLAN PROVIDES ADDITIONAL SECURITY
4. THE MESSAGE BROADCAST INONE GROUP CANNOT BE LISTEN BY ANOTHER GROUPS.
________________________________________
CONFIGURATION VLAN
FIRST STEP
GO TO SWITCH CLI INTERFACE
WE WILL
CONFIGURED VLAN THIS BASED ON YOUR COMPUTER PORTS ATTACHED ON A SWITCH.
WE WILL CONFIGURED VLAN'S
VLAN 10 NAME IT PORTS ASSIGN inter fa0/1-3
VLAN 20 NAME HR PORT ASSIGN inter fa0/4-7
VLAN 30 NAME SALE PORT ASSIGN inter fa0/8-10
SECOND STEP
COMMUNICATION BETWEEN VLAN 10 VLAN 20 AND VLAN 30
__________________________________
FIRST STEP
GO TO SWITCH CONFIGURATION MODE
Switch(config)# Vlan 10
Switch(config)# name it
Switch(config)# vlan 20
Switch(config)# name hr
Switch(config)# vlan 30
Switch(config)# name sale
Switch(config)# inter range fa0/1-3
Switch(config-if-range)# switchport mode access
Switch(config-if-range)# switchport access vlan 10
Switch(config-if-range)# inter range fa0/4-7
Switch(config-if-range)# switchport mode access
Switch(config-if-range)# switchport access vlan 20
Switch(config-if-range)# inter range fa0/8-10
Switch(config-if-range)# switchport mode access
Switch(config-if-range)# switchport access vlan 30
SEE THE VLAN GO TO SWITCH ENABLE MODE AND ENTER THE COMMAND
Switch# show vlan
TO SEE CONFIGURED THE VLAN'S. BUT DIFFERENT VLAN'S PC CANNOT COMMINICATION BETWEEN THEM.
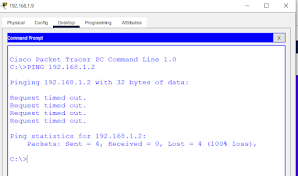
GO TO VLAN 30 LAPTOP AND CLICK DESKTOP AND GO TO COMMAND PORMOT
WE PING THE VLAN 10 PC AND VLAN 30 LAPTOP IP IS 192.168.1.2 AND 192.168.1.9
SO ENTER THE COMMAND
C:\> PING 192.168.1.2
COMMUNICATION BETWEEN VLAN 10 VLAN 20 AND VLAN 30
AGEN GO TO SWITCH CLI INTERFACE AND ENTER THE COMMAND.
Switch(config)# inter range fa0/1-10
Switch(config-if-range)# switchport mode trunk
AND AGAIN PING SAME VLAN 10 AND VLAN 30 DEVICES
C:\> PING 192.168.1.2
COMPLETE THE ALL STEPS AND DONE THE CONFIGURATION.
______________________________________



Comments
Post a Comment