WHAT IS ETHER-CHANNEL
COMBINE THE MULTYPAL PHYSICAL LINKN INTO ONE LOGICALL LINK IS CALLED ETHER CHANNEL.
COMMONLY USE THIS TO INCREASE THE BANDWIDTH OF LAYER 2 TECHNOLOGIES, MEANING ALL TRAFFIC WITHIN YOUR LAN CAN BE INCREASED.
ETHERCHANNEL IS A TECHNOLOGY WHEREIN WE BUNDLE PHYSICAL INTERFACES TOGETHER TO CREATE A SINGLE LOGICAL LINK.
IT IS ALSO KNOWN AS LINK AGGREGATION.
IT PROVIDES FAULT-TOLERANT AND HIGH-SPEED LINKS BETWEEN CISCO SWITCHES AND ROUTERS AND IS OFTEN SEEN IN THE BACKBONE NETWORK.
_________________________
TYPES OF ETHER-CHANNEL
1. STATIC ETHER-CHANNEL
2. DYNAMIC ETHER-CHANNEL
STATIC ETHER-CHANNEL
STATIC LINK AGGREGATION IS A METHOD OF COMBINE OR BINDING OF MULTIPLE SWITCH PORTS OR NICS TO FORM A SINGLE ETHERCHANNEL.
A STATIC LINK AGGREGATION MEANS THAT YOU MANUALLY CONFIGURE THE LINKYOU WISH TO USE AS PART OF YOUR ETHERCHANNEL.
DYNAMIC ETHER-CHANNEL
THERE IS A WAY OF ACQUIRING HIGHER BUNDING BY BANDWITH PORTS TOGETHER.
A BETTER WAY TO DEFINE IT WOULD BE TO SAY IT PERFORMS PORT LINK AGGREGATION.
IT ALLOWS GROUPING OF SEVRAL ETHERNET POERTS TO CREAT ONE LOGIC ETHER-CHANNEL.
IT IS OPEN STANDERD RATIFIED UNDER IEEE802.1D
PROTOCOLS USED IN ETHER-CHANNEL
1. LACP (LINK AGGREGATION CONTROLL PROTOCOL)
2. PAGP (PORT AGGREGATION PROTOCOL)
LACP DIFFERENT PAGP
__________________________
CONFIGURATION
WHEN YOU CONFIGURE "STATIC ETHER-CHANNEL" CHHANEL GROUP MODE IN "ON"
WHEN YOU CONFIGURE "DYNAMIC ETHER-CHANNEL" CHANNEL GROUP MODE IS ONE SWITCH "ACTIVE" AND SECONE SWITCH IS "PASSIVE"
_____________________
NOTE
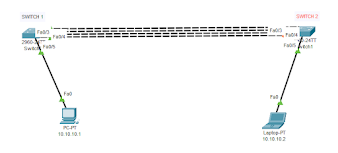
WHEN YOU FIRST TIME ATTACH FOUR LINKS BETWEEN A TWO SWITCH.
ONE OF THE LINKS WILL BE IN COMMUNICATION AND THE OTHER THREE LINKS GOES WILL BE DOWN.
BUT WHEN YOU CONFIGURE THE ETHERCHANNEL, IMMEDIATELY AFTER THAT FOUR LINKS WILL BE UPED.
AND THE COMMUNICATION WILL START AS A FOUR LINKS AND NONE OF THE LINKS WILL BE DOWN.
REQUIREMENT
1. ANY MODEL OF SWITCHE PERFORM ETHER-CHANNEL.
2. FOUR LINKS ATTACHED BETWEEN TWO SWITCHES.
3. ATTACHED LINK INTERFACES IS fa0/1-4 .
STEP 1
CONFIGURE STATIC ETHER-CHANNEL.
STEP 2
CONFIGURE DYNAMIC ETHER-CHANNEL.
___________________________
CONFIGURATION
CONFIGURE STATIC ETHER-CHANNEL
GO TO SWITCH CLI INTERFACE AND GO TO "CONFIGURATION TERMINAL MODE "AND PERFORMS A COMMAND.
Switch(config)# INTER R FA0/1-4
Switch(config-if-range)# CHANNEL-GROUP 2 MODE ON
IF YOU WANT TO SEE IF THE ETHERCHANNEL CONFIGURED IS ALSO CREATED OR NOT..
Switch# show etherchannel
IF YOU WANT TO SEE IF THE WHICH ONE PORTS ASSIGN A ETHERCHANNEL
Switch# show etherchannel summary
Switch# show etherchannel port-channel
SWITCH 2
SAME COMMANDS RUN TO SW1 IN SW2.




Comments
Post a Comment